
A guide to using different kinds of analysis and tracing to reverse engineer software.
How to use Radare2 and various features of x86 assembly to create rough C code for a disassembled binary.
Using Radare2 to find flags in a binary program by reverse engineering or altering behavior.
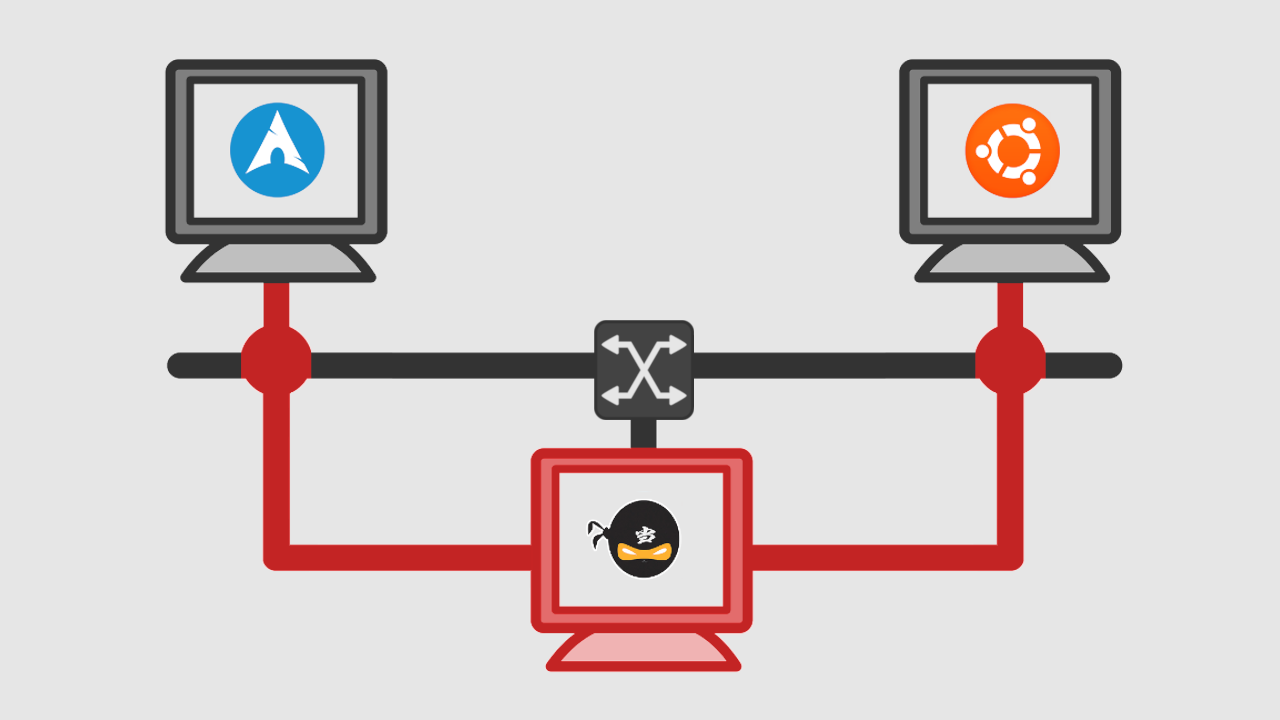
A comprehensive guide to figuring out how a network protocol works and writing your own implementation.